The very real threat of Cyber-attacks Against Nuclear Plants
 Cyber-attacks Against Nuclear Plants: A Disconcerting Threat INFOSEC Institute, Pierluigi Paganini OCTOBER 14, 2016 A cyber-attack against critical infrastructure could cause the paralysis of critical operations with serious consequences for a country and its population.
Cyber-attacks Against Nuclear Plants: A Disconcerting Threat INFOSEC Institute, Pierluigi Paganini OCTOBER 14, 2016 A cyber-attack against critical infrastructure could cause the paralysis of critical operations with serious consequences for a country and its population.
In a worst case scenario, a cyber-attack could affect processes that in case of fault could cause serious damages and consequent losses of human lives.
Let’s think for example to a refinery or a nuclear plant, in both cases; a cyber-attack represents a threat to the infrastructure, its processes, and people that work within.
Nuclear plants are critical components of any countries; critical functions depend on their operations, and an incident could have dramatic effects on the population.
Is a cyber-attack against a nuclear plant a possible event?
Unfortunately, the response is affirmative. Nuclear plants are composed of an impressive number of components such as SCADA/ICS, sensors and legacy systems that could be hit by a hacker.
The most popular case of a cyber-attack against a nuclear plant is Stuxnet, which was launched more than five years ago. Stuxnet is the malware developed by experts from the US and Israel with the intent of destroying the Iranian nuclear program. Nation state hackers hit the plant of Natanz in Iran in 2010 interfering with the nuclear program of the Government of Teheran.
The Stuxnet targeted a grid of 984 converters, the same industrial equipment that international inspectors found out of order when visited the Natanz enrichment facility in late 2009.
The cyber-attack against the Cascade Protection System infects Siemens S7-417 controllers with a matching configuration. The S7-417 is a top-of-the-line industrial controller for big automation tasks. In Natanz, it is used to control the valves and pressure sensors of up to six cascades (or 984 centrifuges) that share common feed, product, and tails stations” states “A Technical Analysis of What Stuxnet’s Creators Tried to Achieve” written by the expert Ralph Langner.
Stuxnet was designed with a number of features that allowed to evade detection; its source code was digitally signed, and the malware uses a man-in-the-middle attack to fool the operators into thinking everything is normal.
Stuxnet is the demonstration that it is possible to use a malicious code to destroy operations at a nuclear plant.
In the last years, security experts and authorities confirmed at least three cases of cyber-attacks against Nuclear plants.
Who are the threat actors that could hit a nuclear plant?
There are many actors, such as cyber criminals, hacktivists, nation-state actors, cyber terrorists and script kiddies, that are threatening critical infrastructure worldwide
Let’s see which are the principal incidents that affected nuclear plants in the last years.
The incidents
According to the Director of the International Atomic Energy Agency (IAEA), Yukiya Amano, a nuclear power plant in Germany suffered a “disruptive” cyber-attack two to three years ago……..
This isn’t the first time that we receive the news of cyber-attacks on nuclear plants. There are three publicly known attacks against nuclear plants:
- Monju NPP (Japan 2014)
- Korea Hydro and Nuclear Power plant (S.Korea 2014)
- Gundremmingen NPP (Germany 2016).
It is likely that Amano was referring the cyber-attack against the Gundremmingen nuclear plant that occurred earlier this year. Security experts, in that case, discovered the presence of the Conficker and Ramnit malware in the target systems……
2014 – Malware based attack hit Japanese Monju Nuclear Power Plant
On January, 2nd 2014 one of the eight computers in the control room at Monju Nuclear Power Plant in Tsuruga, Japan, was compromised by a cyber-attack. The local IT staff discovered that the system in the reactor control room had been accessed over 30 times in a few days. The experts observed the intrusion started after an employee updated a free video playback application running on one of the computers in the plant…….
Cyber-attacks against the organizations operating in the Energy industry were already observed in the past, in 2012 the Japan Atomic Energy Agency was targeted by a cyber-attack that compromised a computer at the JAEA headquarters at Tokaimura by infecting it with malware.
2014 – Nuclear plant in South Korea hacked
In December 2014, the South Koran government revealed that a nuclear plant in the country was hacked. …..
2016 – A malware infected systems at the Gundremmingen nuclear plant in Germany
In April 2016, the German BR24 News Agency reported the news of a computer virus that was discovered at the Gundremmingen nuclear power plant in Germany……..The experts involved in the investigation discovered the presence of the Conficker and W32.Ramnit malware in unit B of the Gundremmingen. Conficker is worm with the ability of rapidly spreading through networks, while W32.Ramnit is a data stealer.
The RWE also added that malware had been found on 18 removable data drives, mainly USB sticks, in office computers maintained separately from the plant’s operating systems………
Conclusions
Cyber-attacks against nuclear power plants and industrial control systems are probably at the top of a long list of potential  disasters that can be caused by hackers.
disasters that can be caused by hackers.
Stuxnet, which targeted nuclear power plants in Iran, is still the most widely publicized threat against such systems.
Security experts are aware of the possibility that hackers could cause serious problems to these critical infrastructures worldwide, for this reason, several governments already launched internal assessments of their infrastructure.
This summer, the European Parliament has passed the new network and information security (NIS) directive that establishes minimum requirements for cyber-security on critical infrastructure operators. http://resources.infosecinstitute.com/cyber-attacks-against-nuclear-plants-a-disconcerting-threat/
No comments yet.
-
Archives
- May 2026 (306)
- April 2026 (356)
- March 2026 (251)
- February 2026 (268)
- January 2026 (308)
- December 2025 (358)
- November 2025 (359)
- October 2025 (376)
- September 2025 (257)
- August 2025 (319)
- July 2025 (230)
- June 2025 (348)
-
Categories
- 1
- 1 NUCLEAR ISSUES
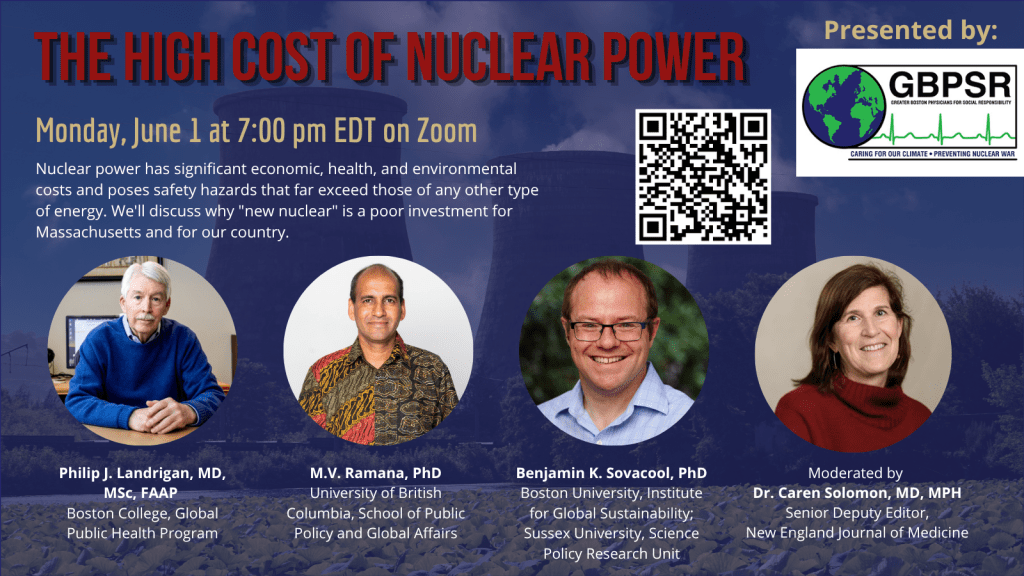
- business and costs
- climate change
- culture and arts
- ENERGY
- environment
- health
- history
- indigenous issues
- Legal
- marketing of nuclear
- media
- opposition to nuclear
- PERSONAL STORIES
- politics
- politics international
- Religion and ethics
- safety
- secrets,lies and civil liberties
- spinbuster
- technology
- Uranium
- wastes
- weapons and war
- Women
- 2 WORLD
- ACTION
- AFRICA
- Atrocities
- AUSTRALIA
- Christina's notes
- Christina's themes
- culture and arts
- Events
- Fuk 2022
- Fuk 2023
- Fukushima 2017
- Fukushima 2018
- fukushima 2019
- Fukushima 2020
- Fukushima 2021
- general
- global warming
- Humour (God we need it)
- Nuclear
- RARE EARTHS
- Reference
- resources – print
- Resources -audiovicual
- Weekly Newsletter
- World
- World Nuclear
- YouTube
-
RSS
Entries RSS
Comments RSS



Leave a comment